Introduction
While OutSystems offers strong native protections against many of the OWASP (Top 10) risks, vulnerabilities can still surface in custom business logic, external integrations, or insecure configurations. That’s where SAST, DAST, and even IAST come into play.
This article explores two essential practices in secure software development: Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST). As a bonus, we will also check Interactive Application Security Testing (IAST). We’ll break down what they are, how they apply to OutSystems, and how to integrate both in your day-to-day development.
Basics
Both SAST and DAST aim to identify vulnerabilities in your application, but they take very different paths to get there.
SAST (Static Application Security Testing)
SAST examines your application’s source code or binaries while they’re at rest. It’s like reviewing blueprints for weaknesses before a building goes up. The key advantage? Early detection. It spots insecure code patterns, improper encryption usage, and more before the app is deployed.
DAST (Dynamic Application Security Testing)
DAST, on the other hand, evaluates your application while it’s running. It acts like a hacker would, probing endpoints for vulnerabilities such as broken authentication or exposed APIs. Think of it as stress-testing a finished building to see where a burglar might break in.
IAST (Interactive Application Security Testing)
For those who were not aware, there’s also IAST (Interactive Application Security Testing), which combines elements of both SAST and DAST. It runs security tests while the application is in use offering deeper insight because it operates from inside the app with an agent.
What is OWASP? And why does it matter?
OWASP (Open Worldwide Application Security Project) is a global nonprofit providing open-source resources for secure development. Its Top 10 list highlights the most critical security risks to web applications, including issues like Broken Authentication and Injection.
OutSystems strengthens security by embedding built-in protections against several OWASP Top 10 threats — including SQL injection, cross-site scripting (XSS), session fixation, cross-site request forgery (CSRF) — while developers remain responsible for best practices in access control, custom code sanitization, and configuration hardening.
Both SAST and DAST help address these risks too. SAST is great for identifying problems like insecure deserialization or cryptographic flaws, while DAST excels at uncovering issues like security misconfigurations or broken access control. IAST helps bridge the gap by confirming vulnerabilities in context.
SAST vs DAST vs IAST: Key differences
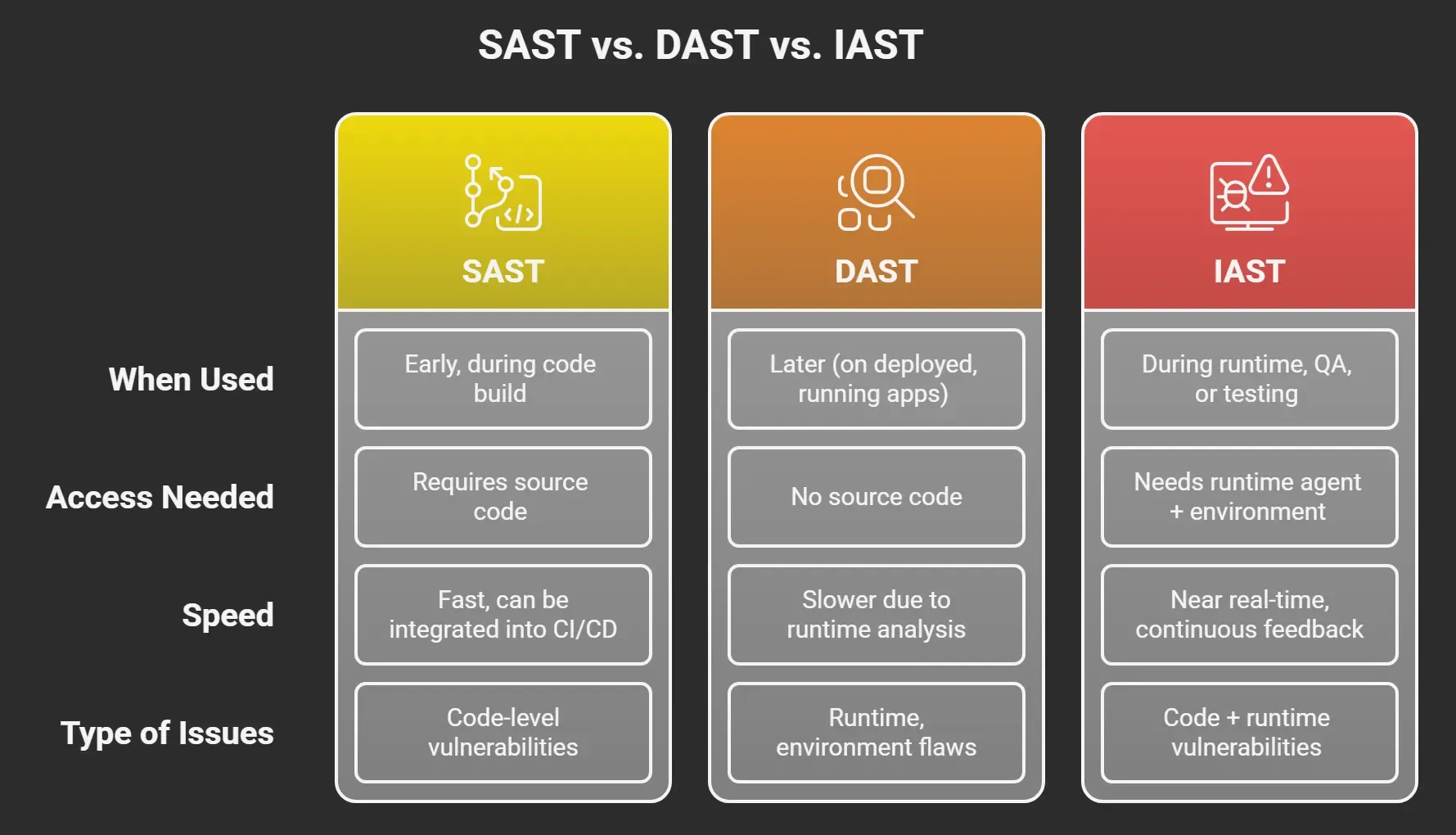
While SAST can detect vulnerable code that could be exploited, DAST confirms whether those vulnerabilities are actually exploitable in production. For example, both might detect an injection issue, but DAST goes one step further by simulating the attack. IAST sits in between, validating vulnerabilities with runtime context, reducing false positives.
Best Practice: Use both (and know when to add IAST)
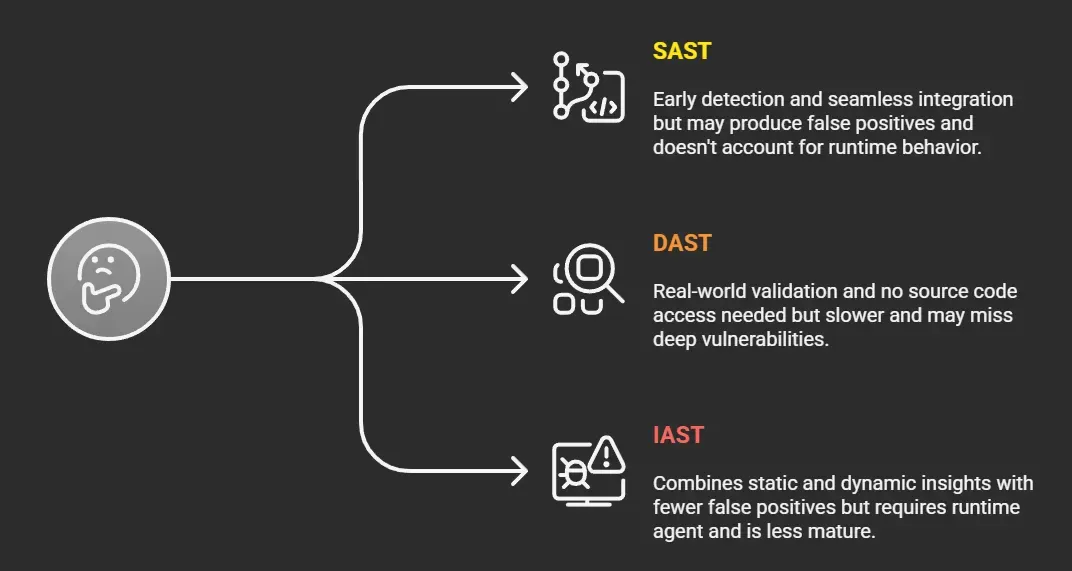
Which security testing method should be used?
Treat SAST and DAST as complementary, not interchangeable tools. Together, they provide comprehensive coverage:
· Run SAST early and often during development (Shift-Left).
· Use DAST before release to validate runtime security and configurations.
Where does IAST fit in? IAST can be useful in QA or staging if you want deeper runtime visibility and developer-friendly feedback. However, it is less mature than SAST and DAST and not yet widely adopted in enterprise security pipelines.
Combined, SAST and DAST create a security feedback loop that protects both code quality and runtime behavior. IAST can add value in certain contexts, but it should be seen as a complement — not a replacement — for the proven SAST and DAST approach.
SAST and DAST in OutSystems
SAST in OutSystems
AI Mentor Studio acts as a core native SAST tool, providing real-time warnings and quality indicators as you develop and is the minimum required tooling everybody needs to use in their OutSystems platform.
OutSystems also has the possibility to export generated code (such as .NET) for static analysis in a CI/CD pipeline, but you need to be on a maturity level where you already have the enterprise-grade SAST tooling (like SonarQube or Veracode) and the CI/CD pipeline running. The export of generated code, requires a custom setup with several LifeTime API calls.
- No external tool is needed for initial SAST — OutSystems provides native checks in Service Studio and AI Mentor Studio
- Set up regular reviews of AI Mentor findings (consider a daily habit, like a morning dashboard check)
- Integrate findings into CI/CD workflows using the OutSystems Lifetime API and/or Mentor Studio API
DAST in OutSystems
DAST tools like Veracode, Invicti, Acunetix, Checkmarx, OWASP ZAP, or many more, scan your deployed application without needing access to the source code. They simulate real-world attacks to validate how your application holds up in runtime scenarios involving sessions, authentication, and data handling. When testing internal applications, make sure the chosen DAST tool is properly whitelisted so it can access the endpoints you want to evaluate.
- Choose a DAST tool like Invicti, Veracode, Checkmarx, Acunetix, or OWASP ZAP
- Run scans against your staging or production environment
- Focus on key OWASP risks: authentication, data exposure, input validation
- Validate session handling, token expiration, and access control
- Combine results with manual testing (e.g. with Burp Suite Pro) for sensitive flows like login, payment, or role management
Code Analysis for Management
Beyond traditional SAST and DAST approaches, many enterprise OutSystems clients rely on BonCode to deliver actionable code analysis tailored for management. Their solution answers two critical questions:
- What are development teams actually building?
- And what is the quality of the software being delivered?
Their platform performs productivity and function point analysis, generates interactive dashboards, and offers independent, fact-based insights into how organizations compare to other leading OutSystems clients.
The tooling does a deep and rich analysis of the delivered OutSystems applications, according to the ISO 25010 standard.
The architecture is visualized and gives an overview of the structure and dependencies across apps and modules.
The technical findings are provided to management via clear and understandable reports and dashboards with drill-downs.
The dashboards & overviews are used to create an overview of the risks & chances for the management, which help them to steer their business & software delivery towards the future.
The export needed for BonCode is fully automated. It will not put any pressure on the development teams. The development teams can keep their focus on the delivery of qualitative software solutions.
Learn more about how BonCode’s independent analysis and how it supports quality and risk in OutSystems landscapes: https://boncode.nl/outsystems/.
Final Words
Security in OutSystems isn’t just about ticking compliance boxes. With tools like AI Mentor Studio and modern third-party tools, SAST and DAST become everyday parts of a developer’s workflow.
While SAST helps you catch issues before they hit production, DAST ensures you’re protected when they do. When used together, they deliver stronger, smarter, and more proactive application security.
As these tools continue to evolve, especially with AI integration, expect security testing in OutSystems to become even more seamless, adaptive, and developer-friendly. The future of secure development is here — make it part of your process from day one.
Hi, I’m Remco, founder and CEO of Evergreen IT.
We build secure, scalable software on the OutSystems High-Performance Low-Code platform. When others stop at challenges, we find solutions.
Need expert support or an independent code review?
Reach out via evergreen-it.nl/contact — your partner for future-proof OutSystems solutions.
